Partners
The Chertoff Group works with a small set of trusted, best-in-class partners to offer technical services that complement our core offerings.
Exiger
The Chertoff Group, a security and growth advisory firm, and Exiger, the SaaS company revolutionizing the way supply chains are managed, have launched a strategic partnership designed to expand the breadth of complementary capabilities available in the market to help federal contractors across the defense industrial base and critical infrastructure illuminate, mitigate and monitor the risk of Foreign Ownership, Control or Influence (FOCI) in their supply chains.
The Chertoff Group and Exiger will offer a combined suite of solutions and services. Exiger brings supply chain mapping technologies, strategic FOCI risk analysis and C-SCRM and SBOM tools. The Chertoff Group provides expert-led regulatory support, national security market expertise, compliance guidance and CFIUS assessments. The offering will target markets with the greatest FOCI risk, including mission critical technologies, companies selling to the U.S. Federal Government, critical minerals and materials, and industries with the greatest exposure to sanctions and the Xinjiang region.
High Value Target
The Chertoff Group and High Value Target have developed a joint offering to deliver cyber resilience managed services. It will help organizations better anticipate, withstand and recover from cyber threats. By identifying high value assets and developing plans to address gaps in resiliency, leaders can be confident in the organization’s ability to recover from a disruptive cyber-attack.
“Our partnership with the Chertoff Group is a significant milestone in Cyber Resilience and will yield immediate benefits for multiple organizations. In a world of finite resources, organizations must precisely identify and protect their high value assets.”
Francesco Chiarini, Founder and Chief Researcher of High Value Target
Tidal Cyber
The Chertoff Group and Tidal Cyber deliver threat-informed defense as a managed service to help enterprise security organizations keep pace more effectively with rapidly evolving cyber threats. This helps organization: Understand which tactics, techniques and procedures (TTPs) matter most as adversary behaviors evolve; Rapidly assess whether existing security products and capabilities adequately cover those evolving TTPs; and Identify solutions that can rapidly address critical coverage gaps as they emerge.
“We are extremely proud to work with The Chertoff Group in this important collaboration,” said Tidal Cyber CEO Rick Gordon. “The Chertoff Group is a globally recognized expert in threat-informed defense. They have helped many of the most sophisticated enterprise security organizations around the world leverage advanced knowledge of adversary behaviors to effectively manage cyber risk.”
Rick Gordon, Tidal Cyber CEO
Second Front
Navigating the Federal market can be challenging and costly with no guarantee of results. The Chertoff Group provides insights, strategy development and market positioning needed to achieve a competitive advantage. Teamed with Second Front Systems’ Game Warden DevSecOps platform and secure cloud hosting environment, the burden of qualifying commercial software with DOD is easier. Software vendors can leverage Second Front’s security controls and DOD-approved platform to accelerate software delivery. The process takes a matter of weeks at a drastically lower cost.
“Our partnership with Chertoff Group provides a proven methodology and trusted technology, to a defense acquisition system which all too often sees great technology languishing in the valley of death.”
Tyler Sweatt, Second Front CEO

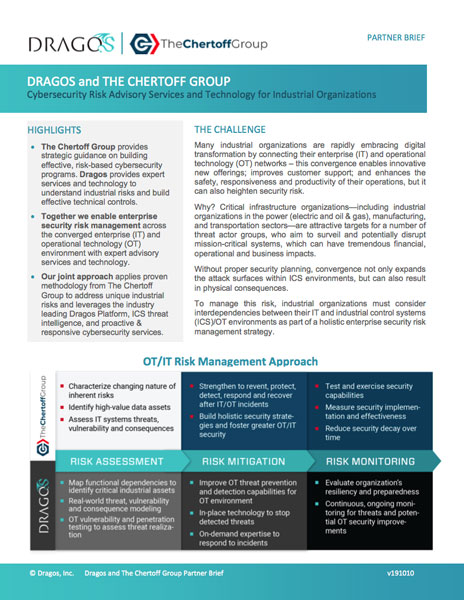
Dragos
The unique architectures and protocols of Industrial Control System (ICS) networks and the developing state of ICS cybersecurity pose new challenges for many asset owners, confronting them with an unclear threat landscape and a shortage of ICS/Operational Technology (OT) security expertise. Our partner Dragos includes industrial security practitioners from the U.S. government cyber teams and around the private sector who provide boots-on-the-ground experience to industrial responders to help them effectively prepare for, contain and remediate potential ICS compromises.
“As we usher in 21st century transportation solutions represented by high speed rail, we believe that the safety of our future passengers is paramount,” said Chertoff Group-Dragos customer Lori Willox, Chief Financial Officer of Texas Central Railway. “We are excited about the Chertoff – Dragos partnership that helps us ensure best-in-class safety and security in our systems through a converged OT/IT cyber risk management assessment.”
Lori Willox, Chief Financial Officer of Texas Central Railway
AttackIQ
Automated validation tools are now available that can run threat tactic-specific diagnostics on an organization’s technology stack. For The Chertoff Group Cyber Risk Diagnostic tool, we work with AttackIQ, using its automated “controls assurance” testing platform, which contains a vast library of mini-testing scripts aligned to a comprehensive knowledge-based of threat actor tactics, techniques and procedures developed by leading U.S. research and development organization MITRE (the MITRE ATT&CKTM framework).
“We have worked with The Chertoff Group for over a year in developing their Cyber Risk Diagnostic, and have used the approach as a proof of concept with multiple customers, receiving overwhelming strong, positive feedback. It is our belief that this solution is a true game-changer in the security industry, providing customers with an unmatched assessment of control effectiveness, targeted training and meaningful security investment justification. ”
Brett Galloway, CEO of AttackIQ

Synopsys Software Integrity Group
The partnership between The Chertoff Group and Synopsys Software Integrity Group helps customers build more secure software faster through a combination of market-leading software security and cyber risk management capabilities. Benefits of our collaborative approach include timely cyber policy insight, unified threat modeling that facilitates better defensive coverage, as well as technical testing and validation to ensure controls are operating as intended. Learn more about our partner Synopsys at https://www.synopsys.com/software-integrity.html
“Organizations are increasingly realizing that software risk equates to business risk. This is a central focus of the partnership between Synopsys and The Chertoff Group, which was born out of a desire to educate organizations on policies and standards and how they can be directly applied to development and deployment teams."
Tom Herrman, Vice President of Channels and Alliances, Synopsys Software Integrity Group